This week, we had the opportunity to host RTS for their 19h30 news program to share our views on the cybersecurity market trends in French-speaking Switzerland. It can be viewed… read more →
Introduction In this article we cover the exploitation of WSUS when used over unsecured HTTP. Specifically, we use socket injection to achieve remote command execution on WSUS clients. For this,… read more →
Insomni’hack 2023 – The Exploit Quest My colleague, Felix Bonningue, and I tackled this challenge, as it seemed quite intriguing. In this challenge, we had to infiltrate a… read more →
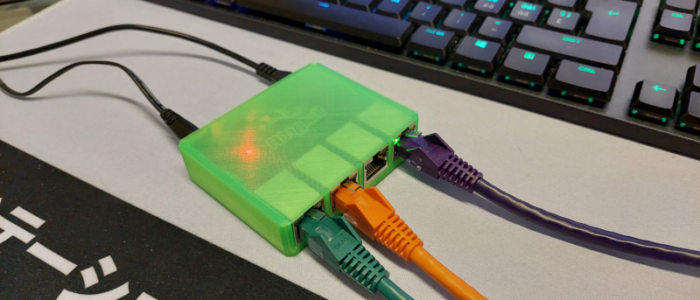
Ethernet ghosting & NAC bypass – A practical overview Introduction Even when provided with direct physical access to the network (client hands you a LAN cable), some security assessments may… read more →
immunIT et ses partenaires ont le plaisir de vous annoncer la 1ère édition de l’immuniDay! Une journée axée autour des dernières innovations en matière de sécurité informatique. Où? Hôtel Warwick,… read more →
Ça déménage chez immunIT ! Afin d’accompagner notre croissance, nous nous sommes installés dans de nouveaux locaux le 1er mai 2022. Un déménagement qui permet à la société d’accueillir de… read more →
The pandemic has increased the use of collaborative tools. Microsoft Teams is no exception: the number of daily active users increased 4 fold between March and October 2020 to reach… read more →
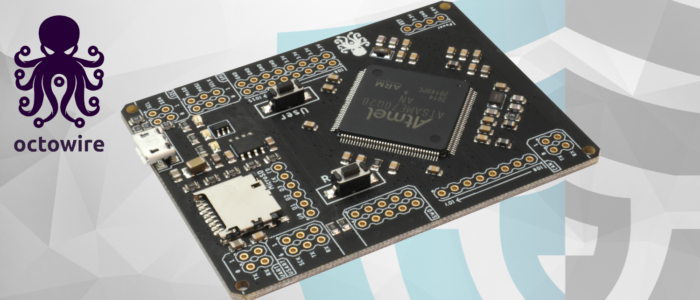
Hello hardware hacker community, As you probably know, we have publicly released the first version of our hardware exploration tool : the Octowire. You can shop it now at :… read more →
Vulnerability Summary Due to discrepancies between the specifications of httpd and Tomcat for path handling, Apache mod_jk Connector 1.2.0 to 1.2.44 access controls to endpoints defined by a JkMount httpd… read more →
Hi everyone, Today, I will introduce you to a new tool, developed for the sake of one of our pentesting engagement, named XIP. XIP claims to provide an efficient way… read more →